Access Control Systems Manufacturers: Elevating Security Equipment with Customized Solutions
Access Control Systems Manufacturers: Elevating Security Equipment with Customized Solutions
Blog Article
Checking Out the Duty of Access Control Solution in Enhancing Security Devices Performance and Effectiveness
Access control systems are progressively identified as important parts in the landscape of security administration, giving a structured method to control accessibility to sensitive areas and info. Their capacity to incorporate with various safety and security innovations, such as security cameras and alarm systems, substantially boosts the total effectiveness and efficiency of safety and security procedures. As organizations navigate the complexities of application and administration, different difficulties develop that warrant factor to consider. What ramifications do these difficulties hold for the future of safety procedures and innovations?
Recognizing Gain Access To Control Systems
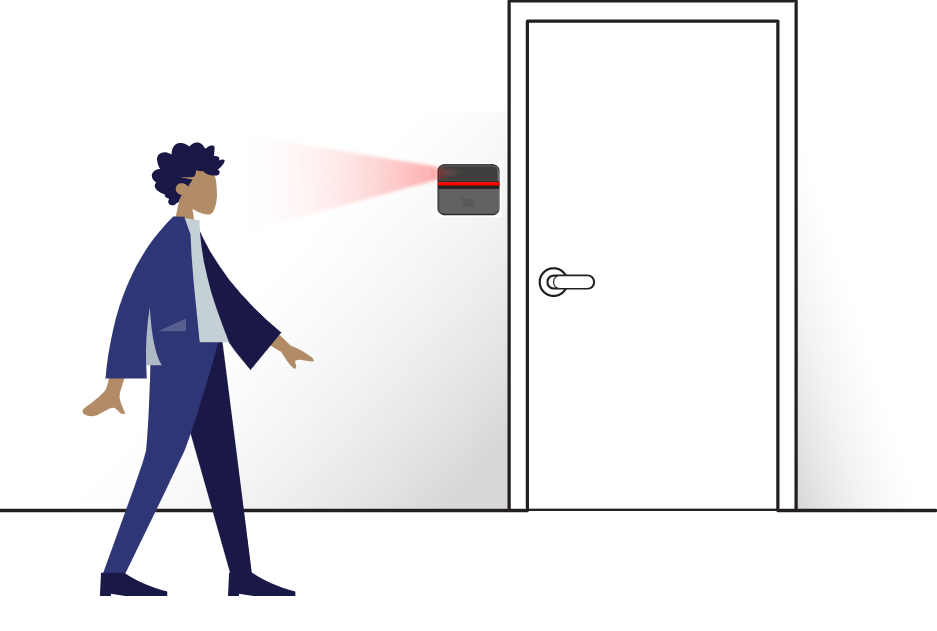
Access control systems play an essential duty in guaranteeing the security of various settings, from company workplaces to sensitive federal government facilities. These systems regulate that can enter or leave an assigned area, therefore securing assets and delicate information. The basic elements of accessibility control systems consist of authorization, verification, and identification processes.
Recognition involves validating an individual's identity, typically with qualifications such as essential cards, biometric information, or passwords. Once determined, verification confirms the individual's right to access, commonly through multi-factor authentication techniques to boost safety and security. Last but not least, authorization identifies the degree of access given, permitting differentiated consents based upon duties within the company.
Access control systems can be categorized into two primary kinds: logical and physical. Physical access control relate to concrete places, while rational gain access to control regulates electronic info systems. Both kinds function synergistically to supply thorough protection solutions.
Integration With Security Technologies
The assimilation of accessibility control systems with other safety and security technologies is essential for developing a holistic protection setting. By integrating gain access to control with video security, invasion detection, and alarm system systems, companies can improve their overall security pose. This interconnected framework allows for real-time surveillance and fast response to protection events, improving situational recognition and operational performance.
For example, incorporating gain access to control with video monitoring enables protection workers to validate gain access to occasions visually, making certain that only accredited individuals are provided entry. When gain access to control systems are connected to alarm systems, any type of unapproved access efforts can cause immediate informs, motivating swift activity.
In addition, the integration of gain access to control with cybersecurity actions is increasingly important in shielding sensitive data and physical possessions. By aligning physical safety and security procedures with IT protection systems, companies can ensure that both electronic and physical access points are kept track of and managed properly.
Advantages of Boosted Security Operations

Additionally, improved safety operations facilitate real-time monitoring and case action. With incorporated systems that encompass surveillance cameras, alarm systems, and gain access to controls, safety and security teams can promptly determine and deal with potential hazards. This positive approach permits for prompt interventions, reducing the likelihood of protection violations and potential losses.
In addition, effective security procedures contribute to a society of security within the organization. Workers are likely to really feel more safe and secure when they understand that durable procedures are in location, leading to boosted morale and performance. The usage of data analytics from gain access to control systems makes see here now it possible for organizations to analyze security patterns, boost policies, and designate sources effectively.
Difficulties and Factors To Consider

Additionally, companies have to address the possibility for information breaches. Access control systems typically take care of sensitive information, and any vulnerabilities might subject this information to unapproved accessibility. access control manufacturers. Guaranteeing robust cybersecurity steps is necessary to shield versus such threats
Customer training is one more important factor to consider. Staff members need to recognize exactly how to utilize gain access to control systems efficiently, as incorrect usage can lead to security gaps. Organizations have to stabilize safety and security with user ease; excessively restrictive accessibility can impede efficiency and lead to workarounds that compromise safety procedures.
Compliance with lawful and regulatory requirements is additionally critical. Organizations must make certain that their gain access to control systems meet market standards and neighborhood laws, which can differ dramatically. The recurring maintenance and monitoring of these systems require specialized sources, making it important for companies to allocate proper spending plans and personnel my review here to make sure long-term efficiency and effectiveness.
Future Patterns in Accessibility Control
Anticipating the future of gain access to control discloses a landscape increasingly shaped by technical advancements and progressing protection requirements. One considerable fad is the integration of man-made knowledge (AI) and artificial intelligence, which boost decision-making capabilities and automate risk detection. These modern technologies enable real-time analysis of access patterns, allowing even more flexible and receptive security steps.
Biometric authentication is likewise getting grip, with innovations in finger print, face acknowledgment, and iris scanning technologies offering enhanced safety and security and user benefit. As these systems end up being a lot more inexpensive and sophisticated, their adoption across numerous fields is anticipated to climb.
An additional arising pattern is the shift towards cloud-based access control systems. These remedies give scalability, remote monitoring, and central data storage, allowing companies to simplify procedures and enhance effectiveness.
Furthermore, the Internet of Points blog (IoT) is readied to reinvent gain access to control by enabling interconnected tools to interact and share data, thereby boosting situational understanding and security responsiveness.
Verdict
In verdict, gain access to control systems significantly boost the efficiency and efficiency of protection devices by facilitating specific identification, verification, and permission processes (security equipment suppliers). Their assimilation with surveillance and security system fosters an aggressive safety and security setting that deals with possible breaches in real-time. While obstacles and considerations exist, the continuous advancement of gain access to control modern technologies promises to additional improve safety procedures. Ultimately, these systems are important to protecting delicate areas and info within companies, ensuring a robust safety structure.
Accessibility control systems are increasingly recognized as vital elements in the landscape of safety monitoring, giving an organized strategy to manage accessibility to delicate locations and details. Physical accessibility control pertains to substantial areas, while sensible accessibility control regulates electronic info systems.The combination of access control systems with other security technologies is essential for creating an all natural protection setting. Accessibility control systems commonly manage sensitive information, and any susceptabilities might subject this data to unapproved accessibility. Organizations should stabilize protection with individual benefit; overly limiting gain access to can hinder performance and lead to workarounds that endanger safety and security protocols.
Report this page